2023 Must-Know Cyber Attack Statistics and Trends
“Attackers often set their sights on healthcare organizations because breaches and incidents have a high impact. Because healthcare is an essential service, organizations are more likely to pay ransoms to provide continuous care when business disruptions can have devastating consequences. Additionally, healthcare organizations possess high-value data, such as personal and financial information. Attackers can often resell records for high prices on the dark web.” Hacking Caused 80% of Healthcare Data Breaches in 2022 (securityintelligence.com)
Cybersecurity Trends & Statistics; More Sophisticated And Persistent Threats So Far In 2023
2023 text written on a flowing binary code background. New Year 2023 celebration concept.
The pace of technological innovation has led to a transformation in many areas of our lives. In 2023, although it is only Spring, the impact of emerging technologies including artificial intelligence/machine learning, 5G, IoT, and quantum are significantly impacting everything connected to the internet.
The introduction of these potentially disruptive technologies do have implications on cybersecurity and the challenges of keeping us safe. In particular, AI is the hot topic of focus as generative artificial intelligence can leverage ChatGPT-powered for code, and ai/machine learning to amplify social engineering capabilities and help identify target vulnerabilities for hackers. These evolving tech trends and statistics are already telling a story for 2023.
As data continues to be produced and stored in greater volumes, and as connectivity greatly expands globally on the internet, the attack surface has become more exploitable with gaps and vulnerabilities for criminal and nation state hackers. And they are taking advantage.
In fact, the global cyber-attacks Rose by 7% already in Q1 2023. “Weekly cyber-attacks have increased worldwide by 7% in Q1 2023 compared to the same period last year, with each firm facing an average of 1248 attacks per week. The figures come from Check Point’s latest research report, which also suggests that the education and research sector experienced the highest number of attacks, rising to an average of 2507 per organization per week (a 15% increase compared to Q1 2022). The Check Point report also shows that 1 in 31 organizations worldwide experienced a ransomware attack weekly over the first quarter of 2023.” Global Cyber Attacks Rise by 7% in Q1 2023 – Infosecurity Magazine (infosecurity-magazine.com)
In addition, key malware statistics for 2023 are adding to cybersecurity difficulties. It is estimated that 560,000 new pieces of malware are detected every day and that there are now more than 1 billion malware programs circulating. This translates to four companies falling victim to ransomware attacks every minute. A Not-So-Common Cold: Malware Statistics in 2023 (dataprot.net)
MORE FROM FORBES ADVISOR
Best High-Yield Savings Accounts Of September 2023
Kevin Payne
Contributor
Best 5% Interest Savings Accounts of September 2023
Cassidy Horton
Contributor
To top it off with more alarming statistics, so far almost 340 million people have been affected by publicly-reported data breaches or leaks in 2023 according to a public data breach tracker created by the U.K. news site The Independent. Cyber Security Today, April 28, 2023 – Data on over 340 million people exposed so far this year | IT World Canada News
Futuristic globalization interface, a sense of science and technology abstract graphics.
SECURING DATA AS VULNERABILITIES AND THE GLOBAL INTERNET ATTACK SURFACE GROWS
Last year, global 5G connections increased 76% in 2022 to 1.05B; 5G penetration hit 32% in North America. Global 5G connections are set to reach 1.9B in 2023. For cybersecurity that means less latency and faster attacks by threat actors. Global 5G Connections Set to Hit 1.9B in 2023 | TV Tech (tvtechnology.com)
Both cyber-attacks and vulnerabilities are expanding. A new report, State of Cyber Assets Report (SCAR) shows released by the cyber asset management company JupiterOne, analyzed over 291 million assets, findings, and policies to determine the current state of enterprise cloud assets. The report found that the number of assets organizations manage on average has increased by 133% year-over-year, from 165,000 in 2022 to 393,419 in 2023. The number of security vulnerabilities has grown disproportionately, jumping up 589%. According to the report, data is the most vulnerable type of asset, accounting for nearly 60% of all security findings.
“The report also highlighted the challenges that security teams are facing, showing that, on average, a security team is responsible for 393,419 assets and attributes, 830,639 potential security risks, and 55,473 policies. This has led to security fatigue and staffing shortages in many organizations. ” Report: Cyber vulnerabilities skyrocket 589%, underscoring importance of cybersecurity | WRAL TechWire
While many industry sectors have been the target of cyber-attacks, including financial, education, and retail, the healthcare industry still is in the cross hairs of criminal hackers. This makes sense as many health institutions still lack the proper investment and expertise in cybersecurity because their funding goes to medical equipment and operations. Criminal hackers tend to go for the low hanging fruit. In the case of healthcare, the liability risks make ransomware a logical means of extortion.
Stethoscope on laptop keyboard, blue lighting
HEALTHCARE STILL HINDERED BY CYBER ATTACKS
“According to the IBM 2022 Cost of a Data Breach report, the healthcare industry is still the costliest industry for a breach — at $10.1 million on average — for the twelfth year in a row. Fortified Health found that 78% of data breaches in 2022 were from hacking and IT incidents, an increase from 45% in 2018. Unauthorized access — the second leading cause — accounted for 38% of incidents in 2018 and now is only responsible for 16%. Other causes noted were theft, loss and improper data disposal.”
“Attackers often set their sights on healthcare organizations because breaches and incidents have a high impact. Because healthcare is an essential service, organizations are more likely to pay ransoms to provide continuous care when business disruptions can have devastating consequences. Additionally, healthcare organizations possess high-value data, such as personal and financial information. Attackers can often resell records for high prices on the dark web.” Hacking Caused 80% of Healthcare Data Breaches in 2022 (securityintelligence.com)
Cyber attack using the phishing technique. Digital illustration.
BE CAREFUL ON WHAT YOU CLICK ON
Phishing is still one of the preferred methods used by criminal hackers. Why, because it is easy to do and successful, especially now that many of the attacks are being automated.
New research shows that up to a half of all HTML email attachments are malicious. “This rate of malicious HTML prevalence is double compared to what it was last year and doesn’t appear to be the result of mass attack campaigns that send the same attachment to a large number of people.”
“Barracuda used its telemetry to perform an analysis in May 2022 and found that 21% of the HTML attachments its products scanned that month were malicious. This was by far the highest malicious-to-clean ratio of any file type sent via email, but it progressively got worse since then, reaching 45.7% in March this year.So, for anyone who receives an HTML attachment via email right now there’s a one in two chance it’s malicious”Attacks increasingly use malicious HTML email attachments | CSO Online
3D rendering Glowing text Ransomware attack on Computer Chipset. spyware, malware, virus Trojan, . [+] hacker attack Concept
RANSOMWARE, THE SCOURGE CONTINUES
Emerging technologies combined with the ability to be paid in cryptocurrencies that are hard to trace has accelerated ransomware attacks in recent years. The trend continues, ransom demands, recovery times, payments and breach lawsuits all on the rise.
“In 2022, we saw increases in average ransom demands, average ransom payments, and average recovery times in most industries,” the report authors wrote. “The lull in ransomware that marked the start of the year is over. Ransomware groups have resumed attacks, and organizations must redouble their efforts to defend themselves against increasing attacks.”
Baker Hostetlet’s Digital Assets and Data Management examined over 1,160 incidents from 2022. While many organizations have bolstered security and resilience, the data shows that threat actors continue to adapt and find footholds onto the network through evasive malware, social engineering, “multi-factor authentication bombing”, and credential stuffing.”
The average time to recover from ransomware rose in nearly every sector, “and in most cases, significantly.” In 2021, the average recovery time for all sectors was just over a week. Last year, the retail, restaurant, and hospitality sectors saw an increase in the average recovery time from 7.8 days in 2021 to 14.9 days in 2022, or a 91% increase.
Healthcare saw a 69% rise in the length of recovery, followed by a 54% uptick for the energy and technology sectors, and 46% in the government industry segments. These increases mirrored a spike in ransom demands in 6 out of 8 industries, with an average payment of $600,688.” Ransom demands, recovery times, payments and breach lawsuits all on the rise | SC Media (scmagazine.com)
For a detailed examination of the ransomware threat, please see my FORBES article Ransomware on A Rampage:
Businessman holding virtual interface panel of global logistics network distribution and . [+] transportation, Smart logistics, Innovation future of transport on large warehouse center background.
THE SUPPLY CHAIN NEEDS CYBERSECURITY BOLSTERING
One of the biggest vulnerabilities for cyber-attacks has been on the supply chain. This was highlighted by the Colonial Pipeline and Solar Winds breaches and many others. It is a formidable task to protect any business or organization from the bast array of cyber- attacks, but when they are part of a supply chain with other parties or vendors, it becomes even a larger challenge. The reality is that 9 out of 10 companies have recently detected software supply chain security risks.
“Reversing Labs Software Supply Chain Risk Survey found that nearly 90% of technology professionals detected significant risks in their software supply chain in the last year. More than 70% said that current application security solutions aren’t providing necessary protections. More than 300 global executives, technology and security professionals at all seniority levels directly responsible for software at enterprise companies, were surveyed for the study.”
“Nearly all respondents (98%) recognized that software supply chain issues pose a significant business risk, citing concerns beyond code with vulnerabilities, secrets exposures, tampering and certificate misconfigurations. Interestingly, more than half of technology professionals (55%) cited secrets leaked through source code as a serious business risk followed by malicious code (52%) and suspicious code (46%).”9 out of 10 companies detected software supply chain security risks | Security Magazine
And data released from Black Kite’s 2023 Ransomware Landscape Report finds the number of ransomware victims announced in March 2023 was nearly double that of April 2022 and 1.6 times higher than the peak month in 2022. Other key findings from April 1, 2022, through March 31, 2023, include:
- The top targeted industries were Manufacturing (19.5%), Professional, Scientific, and Technical Services (15.3%), and Educational Services (6.1%).
- The United States was the top targeted country, accounting for 43% of victim organizations, followed by the UK (5.7%) and Germany (4.4%).
- Ransomware groups tend to target companies with annual revenues of around $50M to $60M, with third-party vendors often being targeted for client information extortion.
- The top ransomware groups during the analysis period included Lockbit (29%), AlphaVM (BlackCat) (8.6%), and Black Basta (7.2%).
Data Breach Button on Computer Keyboard
HIDING BREACHES IS A DANGEROUS POLICY
Because company reputations and stock prices can be impacted by a breach disclosure, that is often a reluctance to report an incursion to the public. New laws that require disclosure, especially in the banking and financial community are on the books and should help to quell this trend, but apparently it has not taken root yet.
“New research released by cybersecurity vendor Bitdefender today surveyed over 400 IT and security professionals who work in companies with 1,000 or more employees. Bitdefender found that 42% of IT and security professionals surveyed had been told to keep breaches confidential — i.e., to cover them up — when they should have been reported. ”
“Perhaps even more shockingly, 29.9% of respondents admitted to actually keeping a breach confidential instead of reporting it. This research highlights that an alarming number of organizations are willing to ignore their obligations to report data breaches to regulators and customers, in an attempt to avoid legal and financial penalties.” A third of organizations admit to covering up data breaches | VentureBeat
This image belongs to the “AI – Artificial Intelligence Background” series
MITIGATING THE EMERGING THREATS
While the threats are more sophisticated and capable, there are some basic cyber-hygiene measures that any company or individual can do to make themselves less of a target. They include:
Multi-factor authentication (MFA): MFA helps limit the possibility of unauthorized access. Enforcing “always-on” MFA through additional physical controls or temporary secondary codes makes life for a cybercriminal more difficult.
Identity and access management: Identity and access management (“IAM”) ensures that only the right people and job roles in your organization can access the tools they need to do their jobs. Through single sign on applications, your organization can manage employee apps without having them log into each app as an administrator.
Strong password management: There are practical remedies to get beyond that bad habit of using easy passwords to crack. Do not use default passwords on your devices and when you do create passwords make them complicated. Consider making them long or using phrases with letters, numbers, and characters.
Protective Tools: for better protection also consider using firewalls, and adding antivirus & intrusion detection software to your devices.
Update and Backup: be sure to update and patch your network in a timely manner and maintain a robust backup program that segments and encrypts sensitive data.
Finally have an Incident Response Plan, anyone in the growing and sophisticated cyber universe can become a victim and attackers always have an asymmetrical advantage.
This is just a small snapshot of some of the trends and statistics that are emerging on the cyber ecosystem in 2023. It is more important than ever to be vigilant and cyber-aware as there is much to be worried about on the cyber-threat horizon.
About The Author:
Chuck Brooks is a globally recognized thought leader and subject matter expert Cybersecurity and Emerging Technologies. Chuck is also an Adjunct Faculty at Georgetown University’s Graduate Cybersecurity Risk Management Program where he teaches courses on risk management, homeland security technologies, and cybersecurity. LinkedIn named Chuck as one of “The Top 5 Tech People to Follow on LinkedIn.” He was named “Cybersecurity Person of the Year for 2022” by The Cyber Express, and as one of the world’s “10 Best Cyber Security and Technology Experts” by Best Rated, as a “Top 50 Global Influencer in Risk, Compliance,” by Thompson Reuters, “Best of The Word in Security” by CISO Platform, and by IFSEC, and Thinkers 360 as the “#2 Global Cybersecurity Influencer.” He was featured in the 2020, 2021, and 2022 Onalytica “Who’s Who in Cybersecurity” He was also named one of the Top 5 Executives to Follow on Cybersecurity by Executive Mosaic, He is a GovCon Expert for Executive Mosaic/GovCon Wire, He is also a Cybersecurity Expert for “The Network” at the Washington Post, Visiting Editor at Homeland Security Today, and a Contributor to Skytop Media, and to FORBES. He has an MA in International relations from the University of Chicago, a BA in Political Science from DePauw University, and a Certificate in International Law from The Hague Academy of International Law.
2023 Must-Know Cyber Attack Statistics and Trends
Cyber attacks have been rated the fifth top rated risk in 2020 and become the new norm across public and private sectors. This risky industry continues to grow in 2023 as IoT cyber attacks alone are expected to double by 2025. Plus, the World Economic Forum’s 2020 Global Risk Report states that the rate of detection (or prosecution) is as low as 0.05 percent in the U.S.
If you are one of the many that run a growing startup, you know the landscape is ever changing and 2020 brought on several changes, to say the least. The pandemic affected all types of businesses — big and small. If anything, the pandemic amplified cybercrime due to the uncertainty around remote working and how to protect your business.
Cybercrime, which includes everything from theft or embezzlement to data hacking and destruction, is up 600% as a result of the COVID-19 pandemic. Nearly every industry has had to embrace new solutions and it forced companies to adapt, quickly.
How can you prepare your startup for data security in 2023 and beyond? In this guide, we dissect the most important cybersecurity statistics, facts, figures, and trends as they relate to your startup.
The average cost of a single ransomware attack is $1.85 million.
Get a free quote today to learn how much a cyber insurance policy could save you.
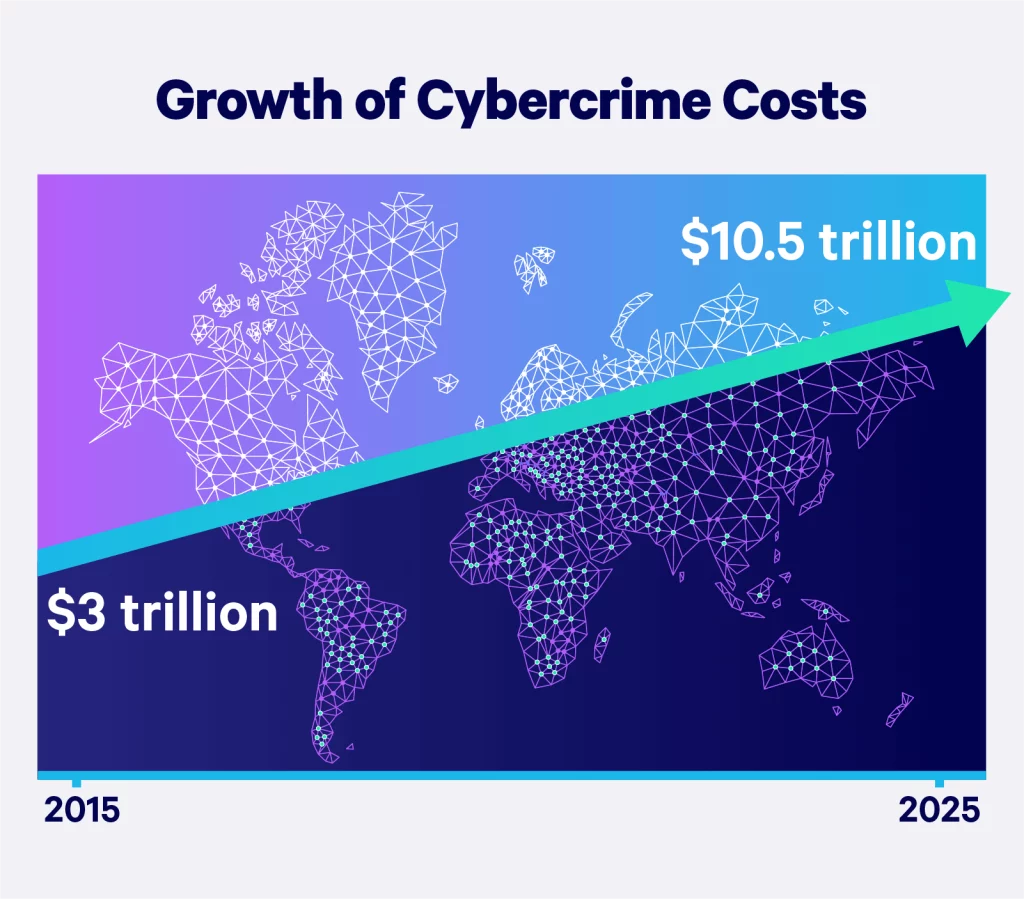
Costs of Cybercrime
Cybercrime will cost companies worldwide an estimated $10.5 trillion annually by 2025, up from $3 trillion in 2015. At a growth rate of 15 percent year over year — Cybersecurity Ventures also reports that cybercrime represents the greatest transfer of economic wealth in history.
Cybercrime for Small and Medium Businesses
Cyber attacks on all businesses, but particularly small to medium sized businesses, are becoming more frequent, targeted, and complex. According to Accenture’s Cost of Cybercrime Study, 43% of cyber attacks are aimed at small businesses, but only 14% are prepared to defend themselves.
Not only does a cyber attack disrupt normal operations, but it may cause damage to important IT assets and infrastructure that can be impossible to recover from without the budget or resources to do so.
Small businesses struggling to defend themselves because of this. According to Ponemon Institute’s State of Cybersecurity Report, small to medium sized business around the globe report recent experiences with cyber attacks:
- Insufficient security measures: 45% say that their processes are ineffective at mitigating attacks.
- Frequency of attacks: 66% have experienced a cyber attack in the past 12 months.
- Background of attacks: 69% say that cyber attacks are becoming more targeted.
The most common types of attacks on small businesses include:
- Phishing/Social Engineering: 57%
- Compromised/Stolen Devices: 33%
- Credential Theft: 30%
By understanding the targets of attacks and consequences, as a business leader you can minimize the potential, gain value in your cybersecurity efforts, and even prevent future attacks.
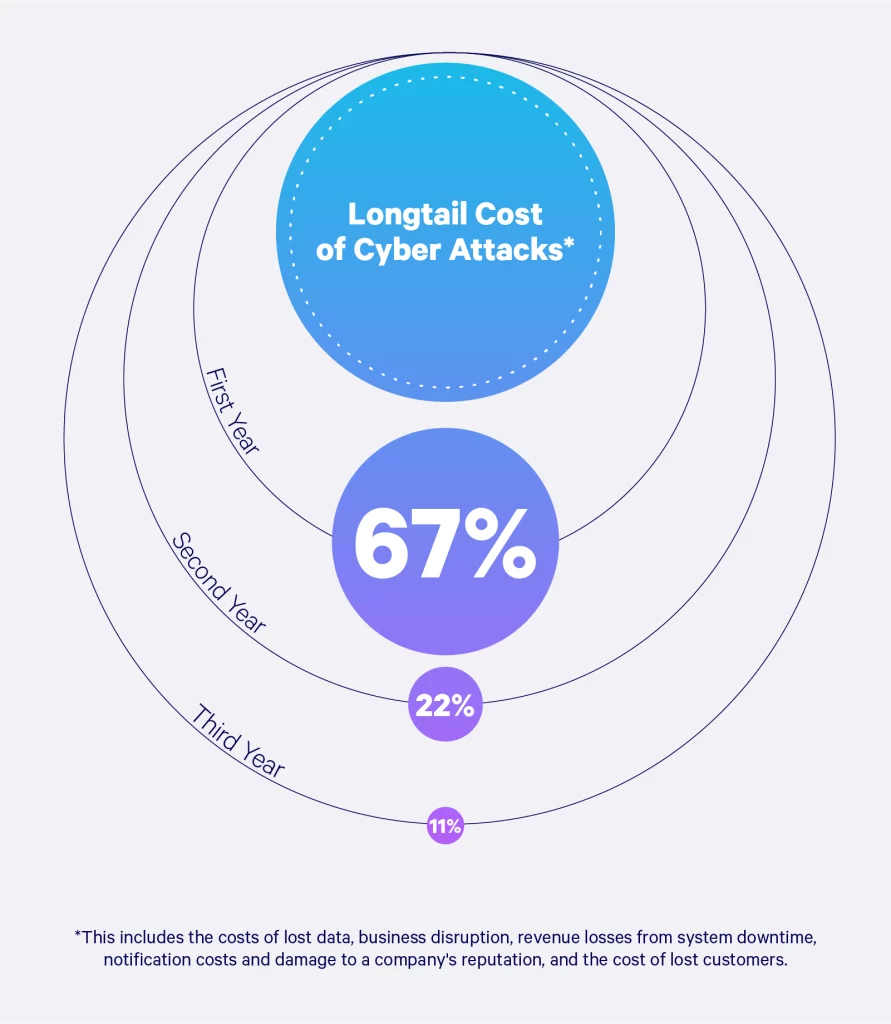
Longtail Cost of Cyber Attacks
The long tail costs of a data breach can extend for months to years and include significant expenses that companies are not aware of or do not anticipate in their planning.
These costs include lost data, business disruption, revenue losses from system downtime, notification costs, or even damage to a brand’s reputation. In the visual below, we outline the impacts a business may face from the first year up to the third year.
Impact and Severity of Cyber Attacks
Cyber attacks can impact an organization in many ways — from minor disruptions in operations to major financial losses. Regardless of the type of cyber attack, every consequence has some form of cost, whether monetary or otherwise.
Consequences of the cybersecurity incident may still impact your business weeks, if not months, later. Below are five areas where your business may suffer:
- Financial losses
- Loss of productivity
- Reputation damage
- Legal liability
- Business continuity problems
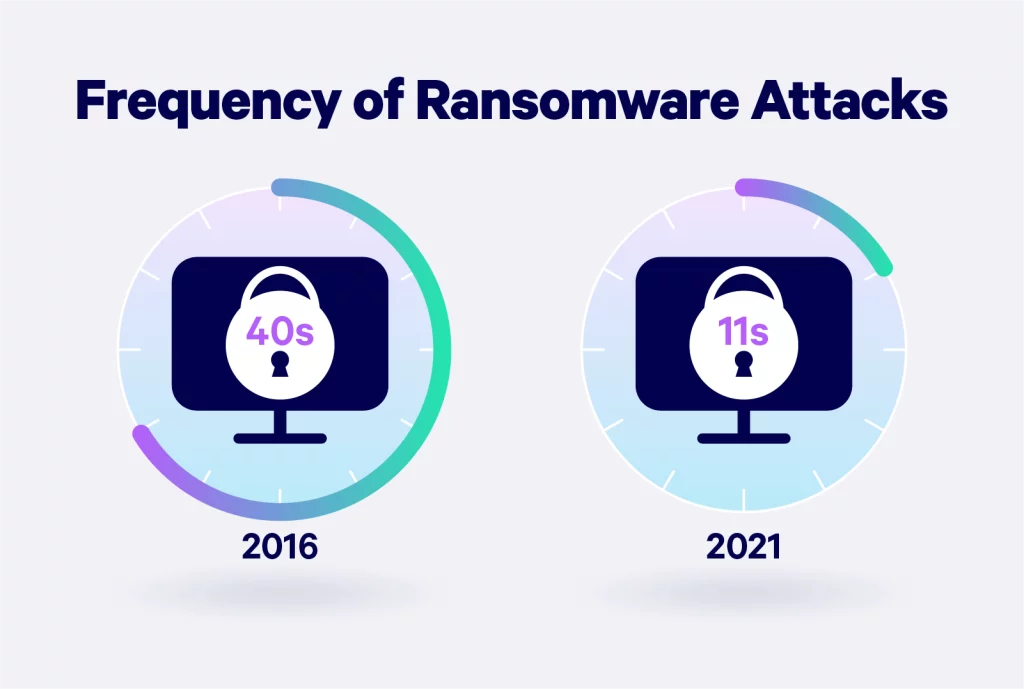
Ransomware attacks are becoming more prevalent as a concern. In 2022, 70% of businesses fell victim to ransomware attacks. This is expected to rise to every 11 seconds by 2021, according to a report by Cybersecurity Ventures. This cyber attack occurs when malicious software is used to restrict access to a computer system or data, until the victim pays ransom requested by the criminal.
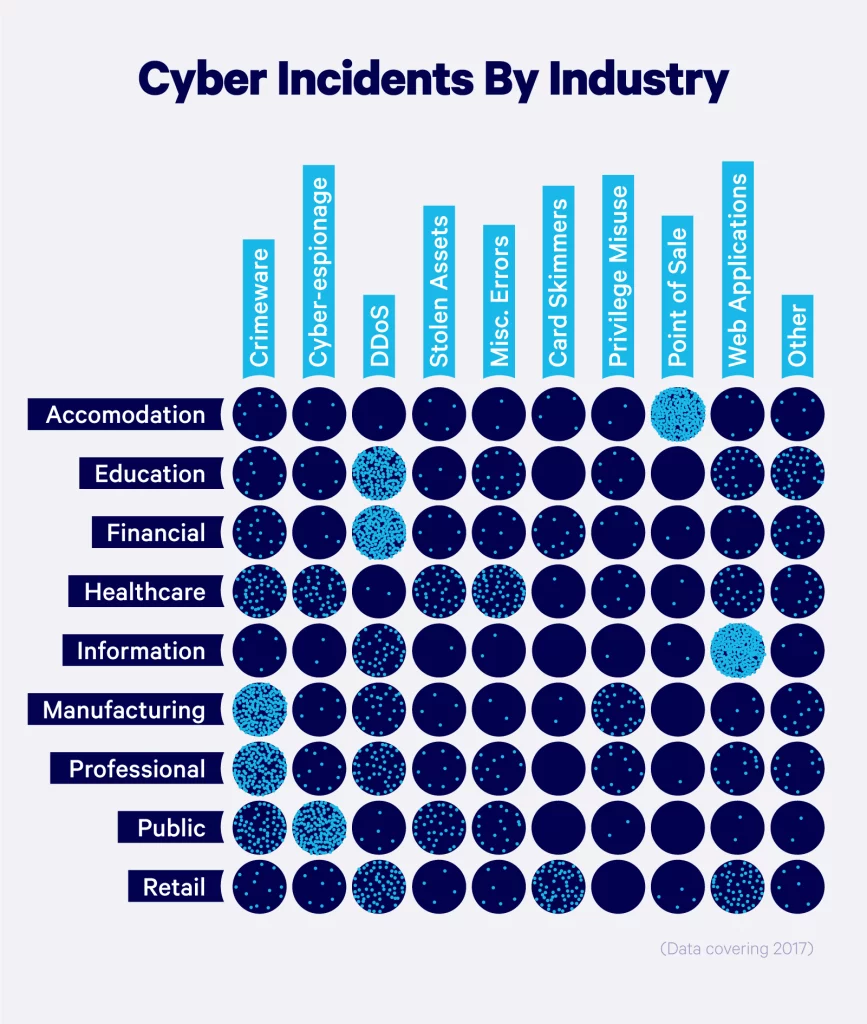
Cyber Attacks by Industry
Some industries are more vulnerable to cyber attacks than others, simply due to the nature of their business. While any industry could be subject to a data breach, those most at risk are businesses that are closely involved with people’s daily lives.
Companies that hold sensitive data or personally identifiable information are common targets for hackers. Types of businesses or organizations that are most vulnerable to cyber attacks include:
- Banks and financial institutions: Contain credit card information, bank account information, and personal customer or client data.
- Healthcare institutions: Repositories for health records, clinical research data, and patient records such as social security numbers, billing information, and insurance claims.
- Corporations: Has inclusive data such as product concepts, intellectual property, marketing strategies, client and employee databases, contract deals, client pitches, and more.
- Higher education: Hold information on enrollment data, academic research, financial records, and personally identifiable information like names, addresses, and billing info.
In the visual below, we break down common types of cyber incidents and the varying impacts on industries.
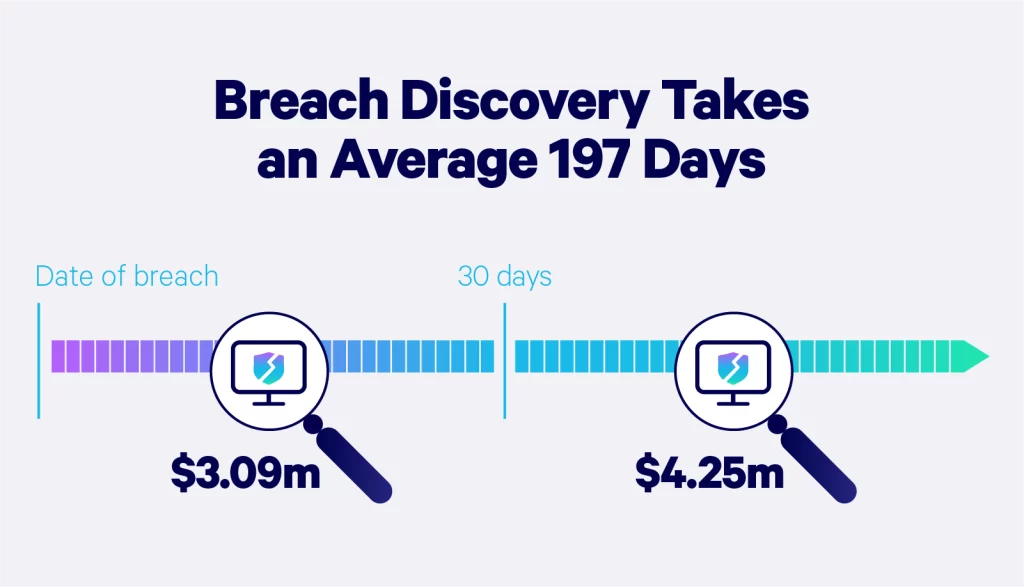
Breach Discovery
Breach discovery is when the company or business becomes aware that the incident occurred. According to IBM, it takes a company 197 days to discover the breach and up to 69 days to contain it.
Companies that contained a breach in less than 30 days saved more than $1 million compared to those that took more than 30 days. A slow response to a data breach can cause even more trouble for your company. It can result in a loss of customer trust, productivity, or major fines.
A data breach response plan is a proactive way to be prepared in the event that a breach does occur. Having a risk management strategy in place to combat incidents such as breaches can minimize the impact on your company and bottom line. An incident response plan, for example, provides guidance for your team during the phases of detection, containment, investigation, remediation, and recovery.
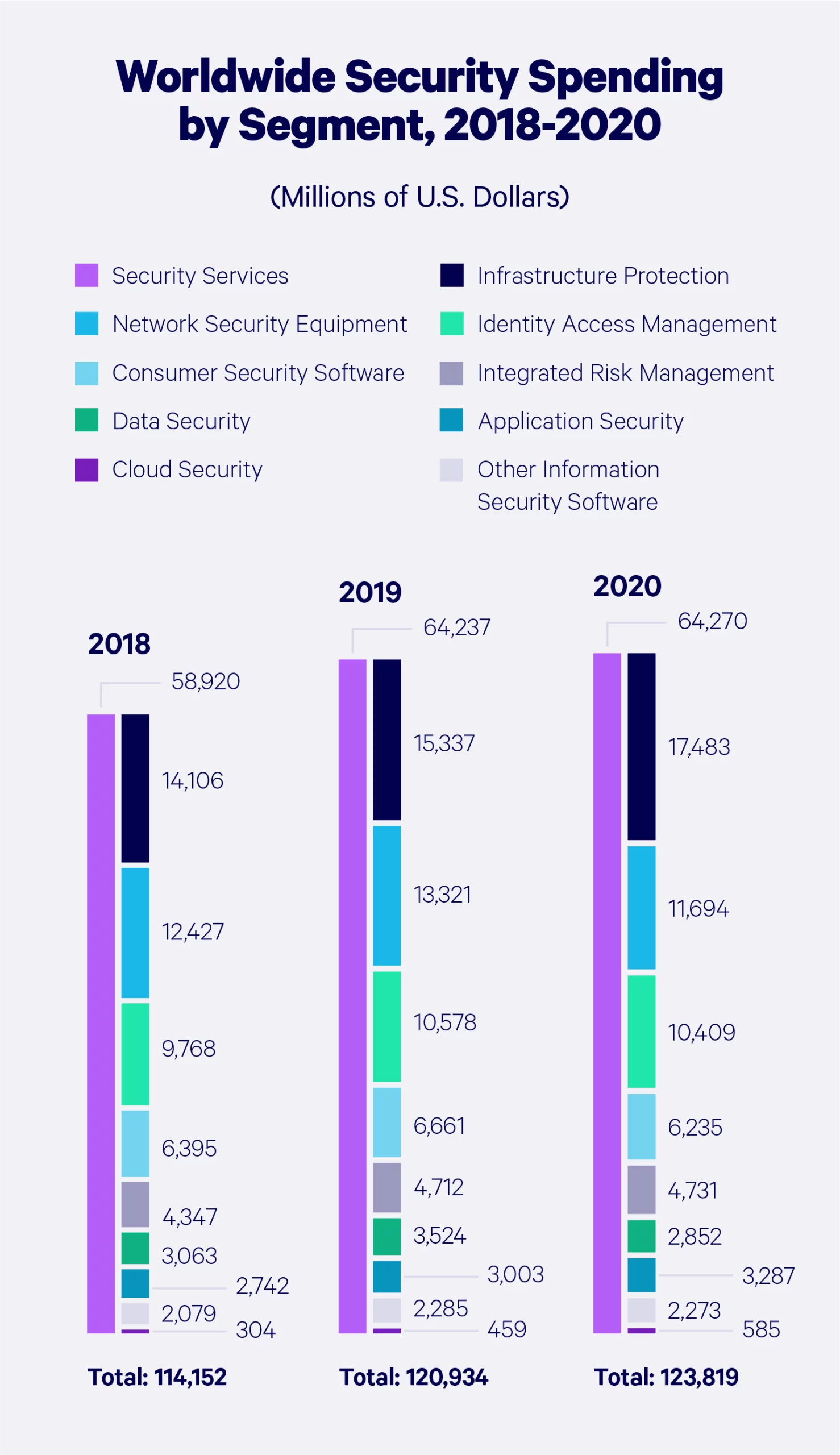
Information Security Spending
Statista Market Report’s revenue in the Cybersecurity market is projected to reach $162 billion in 2023. It is expected to show an annual growth rate from 2023 to 2028 of 9.63%, resulting in a market volume of $256.50 billion by 2028.
Global Security Spending
Let’s take a look at how cybersecurity spending has grown around the globe — broken down by product or service.
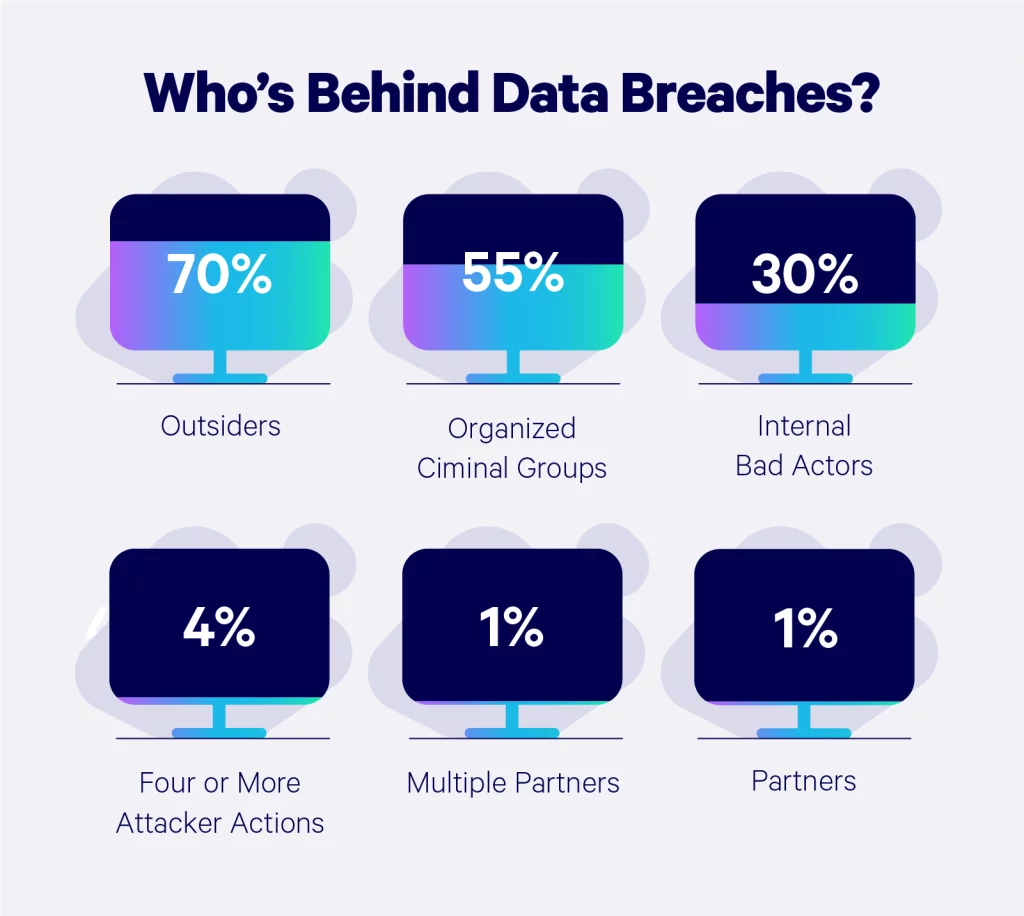
Who’s Behind Data Breaches?
The average person might assume the files on a company database are a bunch of boring documents, but hackers know the hard truth about that hard drive.
According to Verizon’s Data Breach Investigations Report, the majority of cyber attacks are triggered by outsiders, insiders, company partners, organized crime groups, and affiliated groups. We break down the percentages of each:
How to Reduce the Risk of Cyber Attacks
With the increasing threats of hackers mishandling your data, implementing processes to prevent data security breaches is the most responsible course of action after having adequate professional data breach insurance.
Data breach laws vary by state, so depending on where your business is located, there are different factors to take into consideration. Notifications around the breach, what’s covered, and penalties will look different depending on the incidence and state you’re located in.
1. Reduce Data Transfers
Transferring data between business and personal devices is often inevitable as a result of the increasing amount of employees who work remotely. Keeping sensitive data on personal devices significantly increases vulnerability to cyber attacks.
2. Download Carefully
Downloading files from unverified sources can expose your systems and devices to security risks. It’s important to only download files from sources and avoid unnecessary downloads to lower your device susceptibility from malware.
3. Improve Password Security
Password strength is the first line of defense against a variety of attacks. Using strings of symbols that don’t have a meaning, regular password changes and never writing them down or sharing them is a crucial step to protecting your sensitive data.
4. Update Device Software
Software providers work hard on continuously making their software more secure, and regularly installing the latest updates will make your devices less vulnerable to attacks.
5. Monitor for Data Leaks
Regularly monitoring your data and identifying existing leaks will help mitigate the potential fallout from long-term data leakage. Data breach monitoring tools actively monitor and alert you of suspicious activity.
6. Develop a Breach Response Plan
Data breaches can happen to even the most careful and disciplined companies. Establishing a formal plan to manage potential data breach incidents, primary cyber attack response plan, and cyber attack recovery plan will help organizations of any size respond to actual attacks and contain their potential damage.
It’s clear that businesses are under a constant threat of cybercrime and must take steps to defend their data. Don’t wait until it’s too late, take steps today to prevent future data breaches and the consequences that follow. Akin to the need for having adequate cyber liability insurance, having adequate data protection is essential.